Get the best of both TimeLog and Business Central. All relevant data is automatically synchronised and it feels like working in one system.
Looking for easy time tracking integrated with Business Central?
Microsoft Dynamics 365 Business Central combined with TimeLog gives you a cohesive IT landscape and easy, intuitive time tracking and detailed project management.











TimeLog & Business Central unify your business
Are you looking for a complete business system that can connect your IT systems across your entire organisation? Then the integration between TimeLog and Dynamics 365 Business Central might be the solution you've been looking for. Dynamics 365 Business Central is the latest version of Microsoft's ERP solution NAV, which is located in the cloud and is perfect for small and medium-sized businesses.

Use TimeLog's One Click Invoicing. Create invoice drafts in just a few clicks, transfer them to Business Central and speed up your invoicing process.
With easy and intuitive time tracking in TimeLog, your data becomes more accurate and time is recorded on time - increasing your invoicing rate.
Maintain full control. You choose whether Business Central or TimeLog is your primary system and which data to transfer.
Combine a complete ERP cloud solution with easy time tracking
Get all employees to track time with an easy time tracking solution - while getting all the benefits of a complete business system. With TimeLog, each employee can track time at their own pace - ensuring accurate data and fewer barriers when it comes to getting all the hours in the book.


Agile invoicing process?
Yes, please!
With the integration between TimeLog and Dynamics 365 Business Central, you get an integrated solution. Registrations in TimeLog can easily be transferred as an invoice basis to Dynamics 365 Business Central.
If you use our One Click Invoicing, where you produce invoice drafts with a few clicks, these can also be transferred to Business Central.
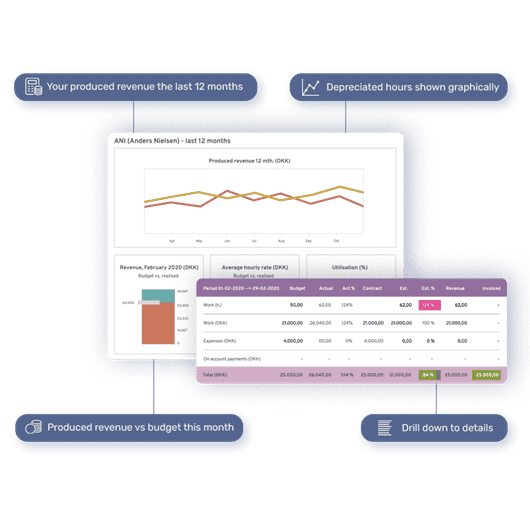
Reporting and analysis without black holes
Get the best of both worlds when it comes to reporting and analysing your key financial figures. Because data between the two systems is synchronised, you have an updated basis for decision-making - without black holes.
In TimeLog, you also have access to a range of standard reports or our REST API, if data needs to be exchanged between other systems or for dashboards.
Do you have questions regarding the Business Central integration or would you like a personal walkthrough?
Price & version
- Requires Monthly subscription to Microsoft Dynamics 365 Business Central
- Requires the Growth-plan or higher
- Available in the cloud and on-premise
Support & installation
- See installationsguide in our help center
- Download at Microsoft AppSource
- Can be installed without help from a consultant
- Do you need help? Contact Customer Success
Permissions & security
- Data & IT-security are a part of our DNA. See how we handle your data
 Read more
Read more
 Read more
Read more

Streamlined project, financial data & payroll with Tripletex & TimeLog
18 min read
 Read more
Read more